Most Common MFT Protocols

Is your company thinking about implementing managed file transfer (MFT) or switching providers? In a situation like this, companies need to consider which protocols they want their MFT solution to support.
Some MFT solutions only support one protocol, while others support a wide variety of protocols. Additionally, each protocol incorporates different functionalities, security levels, technologies, and more.
For an overview of protocols and their intended use cases, as well as insight into which are the most commonly used and other factors to consider when selecting a protocol, continue reading.
What Is MFT?
Managed file transfer (MFT) software is designed to connect a company's information sources and that information's consumers. After the connection between the two entities is built, the two parties can securely move data between each other. Common integration patterns companies may create are often between itself and partners, suppliers, and customers. These patterns include:
• System-to-System file transfer: used as part of internal business processes, keep systems in sync
• Multi-enterprise file transfer: used to connect a business to its ecosystem of business partners, customers, and service providers
• Large file transfer: used for redundancy, DR strategies, and/or aggregation
• Ad hoc file transfer > Human to system, system to human, human to human: used to automate file transfers where one side is a person—used for collaboration/digital teams
As for the future of MFT, the technology will continue to evolve, helping companies scale, and improve agility, response times, governance, and reliability.
What Are Protocols?
Protocols are the technologies that enable two parties to communicate. Think of each protocol as a language. Both parties in a transaction must use the same protocol (language) to understand each other. Each data transfer protocol has its own set of advantages and limitations.
Companies need to understand their current and future file transfer needs as it will help them select the best protocols for connectivity, standardization, scalability, stability, and security. When picking a protocol, companies should consider factors such as file size, volume, frequency, certificate management, and the associated functionality requirements. Lastly, depending on a business's needs, supporting several protocols may be needed.
Why You Need to Support More than One Protocol
For companies looking to implement MFT for the first time or that are searching for a new MFT provider, the solution must support multiple protocols. This is because there are a variety of protocols that trading partners may use depending on their preferences and needs.
Therefore, if companies want to maximize their number of business opportunities, they need to support all the most common protocols, as well as the protocols most used in their industry. This will enable them to communicate and conduct business with the largest number of trading partners possible, which equates to more revenue. Otherwise, companies will lose out on potential business since they will not be able to accommodate the protocol requests of business partners.
Lastly, companies should future-proof their integration infrastructure by considering which protocols they need now and which they may need in the future. This helps businesses avoid having to switch MFT providers which requires time, money, and effort.
The Most Common Data Transfer Protocols
To get an idea of which protocols an MFT solution should support, we list and explain some of the most commonly used protocols below.
STANDARD PROTOCOLS
1. AS2 (Applicability Statement 2)
AS2 is a standard by which users transfer EDI or other data, such as Extensible Markup Language (XML) or plain text documents, over the Internet using HTTP and HTTPs. AS2 offers increased verification and security that is achieved using receipts, digital signatures, and file encryption. Its transactions and acknowledgments occur in real-time, increasing the efficiency of document exchanges.
2. AS4 (Applicability Statement 4)
AS4 guidance is a standardized methodology for the secure and document-agnostic exchange of B2B payloads using Web Services. The profile focuses on providing an entry-level onramp for Web Services B2B messaging.
3. ebMS 2.0 (ebXML Messaging Service)
ebXML Messaging focuses on the means to transmit a payload from one party to another, possibly via intermediaries. This protocol is an attempt to standardize the way B2B transactions are transmitted in a way that includes all sizes of companies
4. FTP (File Transfer Protocol)
FTP is an application protocol that uses the Internet's Transmission Control Protocol (TCP)/IP protocols. FTP is commonly used to transfer Web page files from their creator to the computer that acts as their server for everyone on the Internet. It's also used to download programs and other files to your computer from other servers.
5. FTPs (File Transfer Protocol Secure — aka FTP over SSL)
FTPs is a protocol for transferring files using Secure Sockets Layer (SSL) to secure the commands and data that are being transferred between the client and the server.
6. SSH FTP (Secure Shell File Transfer Protocol — aka SFTP)
SSH FTP uses SSH to transfer files and requires that the client be authenticated by the server. Commands and data are encrypted to prevent passwords and other sensitive information from being exposed to the network in plain text.
7. HTTP (Hypertext Transfer Protocol)
The foundation of data communication for the Internet, this application protocol is the one to exchange or transfer hypertext. HTTP defines how messages are formatted and transmitted, and what actions Web servers and browsers take in response to various commands.
8. HTTPs (Hypertext Transfer Protocol Secure — aka HTTP over SSL)
HTTPs is a secure version of HTTP and it allows secure e-commerce transactions. Using HTTPs, computers agree on a code between them on a Secure Sockets Layer, and then they scramble the messages using that code so that no one in between can read them.
9. MLLP (Minimal Lower Layer Protocol)
Commonly used within the HL7 (Health Level Seven) community for transferring HL7 messages, MLLP provides a minimalistic session-layer framing protocol. MLLP supports only direct connections between a sender and a receiver, and there is no authentication process.
10. OFTP (Odette File Transfer Protocol)
Established by Odette, the European automotive standards body, OFTP is the most prolific protocol inside Europe for the exchange of EDI data, in particular for the automotive industry, and was initially designed to work over an X.25 network.
11. OFTP2 (Odette File Transfer Protocol 2)
This advanced version of OFTP is mainly intended for secure data exchange over the Internet, where security is enhanced using encryption methods and digital certificates.
12. RNIF (RosettaNet Implementation Framework)
This protocol defines how systems transport a RosettaNet message. RosettaNet is a set of XML standards for integrating business processes between companies, and RNIF is a robust transfer, routing, packaging, and security standard.
13. SMTP (Simple Mail Transfer Protocol)
This is a protocol for sending email messages between servers. Most e-mail systems that send mail over the Internet use SMTP to send messages from one server to another; the messages can then be retrieved with an e-mail client.
14. SMTPs (Simple Mail Transfer Protocol Secure — aka SMTP over SSL)
This is a method for securing SMTP with transport layer security. It is intended to provide authentication of the communication partners. SMTPs is not an extension of SMTP; it is just a way to secure SMTP at the transport layer.
15. WS (Web Services)
Web services are XML-based information exchange systems that use the Internet for direct application-to-application interaction. These systems can include programs, objects, messages, or documents.
Complete MFT Implementation Guide
FILE ACCELERATION PROTOCOLS
1. Cleo Jetsonic„¢
This transfer technology enables customers to achieve high-speed transfers using proprietary Cleo technology based on parallel TCP. Based on the core Cleo technology stack, this solution enables the fastest transfer times in the industry — of any TCP or UDP-based technology — for any file size with a high-level of security.
This enables customers to control primary network characteristics for slowdowns, like network speed and latency as well as secondary characteristics, such as background traffic, jitter, and data loss.
MESSAGE QUEUE PROTOCOLS
1. IBM® WebSphere® MQ
IBM's proprietary technology is a robust messaging middleware that simplifies and accelerates the integration of diverse applications and business data across multiple platforms.
2. AMQP
The Advanced Message Queuing Protocol (AMQP) is an open standard protocol that works at the application layer. AMQP allows message orientation, queuing, and routing, while providing interoperability, reliability, and security for sending and receiving messages between businesses and applications
3. Kafka
Apache Kafka is an open-source streaming message broker and choice for many organizations for data streaming to data warehouses and building ingestion pipelines to data lakes. Compared to traditional message brokers, Kafta offers improvements including throughput, partitioning, replication, and fault tolerance for use cases including traditional message brokering, real-time data streaming, log, or event data aggregation, as well as activity and event monitoring.
SECURITY PROTOCOLS
1. LDAP
The Lightweight Directory Access Protocol (LDAP) is TCP/IP-based open-source protocol that supports two-factor authentication through the simple authentication and security layer. Dating to the late 1980s, the most recent specification version was established in 1997. LDAP allows businesses to better manage hierarchical enterprise directories by allowing user, system, network, services, and application data to be securely shared.
2. ICAP
The Internet Content Adaptation Protocol (ICAP) provides simple vectoring for HTTP-based messages or content. The ICAP standard was proposed in 1999 and later specified in RFC 3507. The lightweight protocol can be used to extend security capabilities in file-based integration scenarios such as connecting dataflows to antivirus scanning and quarantine applications. ICAP also commonly supports business content filtering and data loss prevention (DLP) use cases.
3. SAML
Security Assertion Markup Language (SAML) is an XML-based communication framework developed by OASIS for federated identity management and to allow businesses to securely exchange identity and authentication information between a security system and trusted applications.
Additional Considerations
There are a few other considerations for companies to explore before selecting a protocol(s). By assessing an organization's specific needs and wants, as well as assessing the factors listed below, companies can narrow down which protocols are most suitable for their requirements.
Message Size
Determining the range in file sizes a company sends/receives will illuminate compatible protocols.
Compression
Compression reduces a file's size before it is sent to a recipient, thus reducing bandwidth usage and file transfer time.
Speed
The amount of overhead, network condition, bandwidth, and latency all have a compounding impact on protocol performance.
Certificate Management
Digital certificates enable trading partners to conduct business together. However, managing them can be cumbersome when multiple partners require secure connectivity. Using automation to schedule renewals, receive expiration notices, and be proactive when it comes to expiring certificates helps avoid system downtime and lost business.
Restart
Particularly useful for large file transfers, restart capabilities enable protocols to restore a failed or interrupted file transfer from the point it stopped, compared to restarting the transfer from the beginning.
Certification
Certification with governing bodies or interoperability testing groups ensures solid protocol performance and reduces setup time—when both the sending and receiving parties are utilizing the same specifications and optional protocol functionality.
Firewall Friendly
Protocols that change ports or use port ranges often require greater firewall configuration. Meanwhile, protocols identified as "firewall friendly" tend to provide easier firewall configuration.
Architecture
Protocol architecture determines how a protocol communicates from point-to-point. The two main architectural approaches are:
Peer-to-Peer
Sometimes referred to as push/push, these protocols work by allowing simultaneous traffic flow from sender to receiver, while file transfers are always initiated from the side that has the data. Peer-to-peer protocols allow for real-time automation on both ends of the connection and require both sides to be in a constant listening state to receive files in real-time.
Client-Server
Sometimes referred to as push/pull, these protocols and associated file transfers are always initiated from the client side. This requires the server to be in a constant listening state but does not require the client to do the same. Client-server protocols require fewer configurations on the client side and are more widely used for date/time or batch-based file transfers.
When assessing the architecture of MFT solutions and their supported protocols, companies should also research the following for each potential solution:
• Is there no single point of failure?
• Is there a large throughput capability?
• Is there two-tier architecture for secure DMZ streaming?
• Is there easy integration with corporate infrastructure?
• Is there a built-in configuration sync?
• Is it built with virtualization in mind?
• Is it easy and linear to scale?
• Is it extremely secure?
A solution that answers yes to all the above questions is likely a great MFT option to consider.
-
How Cleo Can Help
Overall, data transport and MFT protocols act as a set of rules that enable businesses to successfully connect and send data internally from point to point, and to other external businesses and entities. In doing so, companies automate transactions, share business intelligence, and create value.
So, what if you could support all of the leading market protocols with one easy-to-use product? What if the support enabled larger files, automated certificate exchange, faster onboarding, and easier trading partner community management?
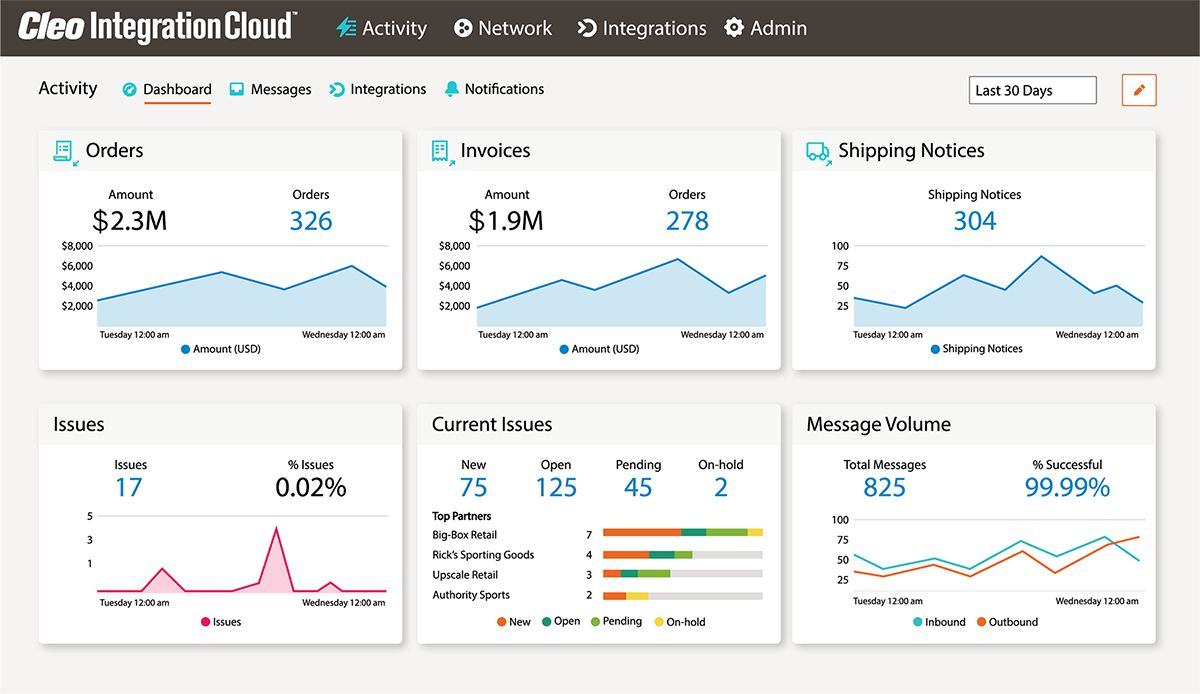
With Cleo, you can do just that. Our Cleo Integration Cloud solution, CIC MFT, supports the widest array of transfer protocols so your company can connect with current trading partners, as well as new partners in the future.
B2B/MFT/EDI
Infrastructure
|
Identity & Access Management Anti-virus Ad Hoc
Storage
Extensibility |
For more information on how to reliably manage all of your organization's data transfer needs using Cleo's extensive protocol expertise, contact us at sales@cleo.com, +1.815.282.7695, or submit a callback request.

About Cleo