Blog: File Sharing Security Risks & Tips on Secure File Exchange

Today’s pace of business requires organizations to manage, control, and govern every ad hoc data flow across systems, teams, and ecosystem partners. However, the file sizes, data formats, and the sheer volume of data flowing through a business require enterprises to have cloud-based secure file transfer technology in place to ensure that business data can flow freely and also remain secure in motion and at rest.
But if IT departments don’t provide the secure file transfer service capabilities employees require, they’ll just download something that does. And such “shadow IT” scenarios present a variety of security, governance, and control challenges that could cost your business.
To fully understand why it is important to have an enterprise-grade, cloud-based secure file transfer tool, it’s important to recognize the risks if you don’t.
Use this guide to learn how to evaluate enterprise file sharing tools:
- What is File Sharing?
- What is Secure File Sharing?
- File-Sharing Security Risks
- Outdated Methods for File Sharing
- Why You Need a Cloud-Based Secure File Transfer Solution
- The Best File Sharing Platform
What is File Sharing?
File sharing is the practice of sharing or enabling access to digital media, including documents, video files, graphics, etc. When you move one or more files from your local computer to another computer or a remote location, you have engaged in a file-sharing process.
File sharing methods:
- Removable storage devices
- USB - Universal Serial Bus
- Centralized servers on computer networks
- All users connect to a single server
- Web-based hyperlinked documents
- Google Docs, Microsoft Online, etc.
- Distributed peer-to-peer networks
What is Secure File Sharing?
Secure file sharing is the process of sharing files securely or privately. Secure file sharing allows files to be shared between different users or organizations within a protected mode that is secure from intruders and unauthorized users.
Secure file sharing is usually done by encrypting the file while at rest or in-flight to its destination. Most secure file sharing services or software providers enable securing file sharing by restricting access to the file, allowing only authorized personnel to access, view, or download the file.
File-Sharing Security Risks
Why the need for a secure file sharing solution?
In modern enterprises, it is a necessity to have a secure file exchange platform in place that can be relied upon. And while as always, security is of the utmost importance, enterprises must also find a file-sharing platform that is easy-to-use and adaptable. When companies don’t provide an adequate option, that’s when end users go find their own consumer-grade solutions to use.
The file-sharing market is loaded with vendors that promise that their tool is the very best and most reliable option. However, there are some important differences between enterprise-grade file sharing solutions – those built specifically with business data exchange in mind – and the cloud-based, consumer-grade file-sharing options meant to share large files with friends and family.
What are the risks of sharing files?
1. Lack of Control Over Data
One drawback of most consumer-grade file-sharing options is that companies simply do not have the necessary control over their data. When employees go downloading these consumer tools and using them to share with external entities, they are taking business information outside the company’s IT scope, which means it is also out of the IT department’s control for security and integration purposes. Additionally, many companies have run into security breaches because employees use these personal file-sharing tools on work-issued devices, and open up another vulnerability point of your business network.
2. Lack of Visibility into Data Flows
A cloud-based consumer file-sharing tool used outside the scope of your IT department hinders comprehensive visibility into companywide information exchanges. Without visibility into business data flows, then, IT personnel cannot adequately track the files entering and leaving the company. This lack of transparency inhibits your organization’s ability to ensure compliance with internal policies or with external mandates and agreements, and it raises risks of penalties, fines, and threats to company credibility.
3. Lax BYOD Policies
Many organizations have established a bring-your-own-device (BYOD) policy, which essentially allows employees to bring their personal devices to use and access on a secure corporate network. But many BYOD policies aren’t properly enforced and can spur numerous security issues for IT when the user mixes business and personal data sharing. Additionally, while BYOD policies tend to save organizations money and the added expense of purchasing new equipment, they also present security risks when devices are stolen, lost, or misused and potentially sensitive data is exposed.
Outdated Methods for File Sharing
Today’s file-sharing options have gotten more agile, flexible, and most secure than previous methods. In fact, some of the file-sharing solutions of yesterday now seem downright outdated and would never suffice to meet the stringent security requirement of the modern enterprise.
1. Traditional Mail/Paper Documents
Who has the time to sit around and wait for something to be delivered via snail mail? Timeliness is the name of the game today, and everyone in an enterprise from top-level execs to IT admins needs their information delivered as quickly as possible. Additionally, manually filing important data can create problems because there is just so much information, so it is not only easy to lose track of these files, but it becomes dependent on individuals to remember the name of files and their storage locations.
Traditionally filed documents can very easily spiral into disorganized chaos within an enterprise. It is very easy for something to get mislabeled, or placed in the wrong folder, and then how is an enterprise supposed to access that information when it truly needs it? Manually filing documents also does not allow for cross-file data integration and data sharing, a must in today’s enterprise. And if files are not integrated with a database, an enterprise risks duplication of data.
2. Fax
Surprisingly, many companies still do rely on fax machines to transfer or receive important documents, particularly in the healthcare, education, and government sectors. The belief is that fax machines are more secure than email, but unless there are encryption and decryption set on both ends of the phone line, that more than likely is not the case. Old-school fax machines also waste paper, take longer to send or receive a document, and are generally inefficient compared with the electronic file transfer solutions that are now widely available. As an alternative, computer-based e-fax solutions allow businesses and organizations to send and receive faxes electronically and integrate digital faxes with back-end systems including EHR or ERP, for instance.
3. USB drives
Cloud services have evolved, but there are still many companies and individuals that rely on USB drives in today’s modern enterprise. While it is certainly understandable why it is hard to let go of that small little device in your pocket, there are several drawbacks to using a USB drive. The first drawback is because these are so small, they are very easy to misplace – or even lose completely. For someone who keeps very sensitive information on a USB drive, if that drive isn’t backed up properly, and the device is lost, so is the sensitive or proprietary information on it.
Another drawback to using a USB drive is that most people do not place any level of encryption on their devices, increasing the risk of piracy and/or theft. Lastly, because the USB is a physical device, for most users, it is inconvenient to store the USB device in a separate location than the primary computer it is used on. So, the USB device is not likely to even be backed up, so in the event of a disaster or theft, both copies of the data would be destroyed and unlikely to be recovered.
4. Cloud file-sharing services
No, the cloud is not outdated. Not by any means, in fact. However, there are questions around data security that enterprises must be aware of if they choose a cloud-based secure file transfer solution. First, cloud breaches do happen. More and more the unthinkable occurrence of a breach or malicious attack must be considered thinkable. Therefore enterprises need to have a plan in place not if but for when the unthinkable happens. Next, consider whether a public cloud solution provides ample enough security to meet emerging and evolving enterprise requirements. Finally, due to the ubiquity of file-sharing use cases and the expectation for ease of use, many business users will find a way to share files regardless of security considerations. This often results in shadow IT.
Complete MFT Implementation Guide
Here are some of the more popular personal file sharing options and greatest culprits of shadow IT:
- Amazon Drive
- Dropbox
- Google Drive
- Apple iCloud Drive
- Microsoft OneDrive
- ShareFile
While cloud-based secure file transfer sharing is easy, consider the following potential data mishaps:
1) An employee circumvents email restrictions on file size by sending a file-sharing link, accidentally exposing the PHI of a patient
2) A popular file-sharing app granted itself system admin rights and the ability to control Apple computers without first seeking to gain user permission
Sound farfetched? Well, both of these things actually happened. Kaiser Permanente was forced to notify 600 members of a breach after patient names, medical record numbers, and medical procedures were exposed through a Dropbox link shared via email. And in 2016, it was reported that Dropbox was automatically overriding OS X user preferences and gaining system accessibility, a security issue that was eventually tackled by Apple, not Dropbox.
While the cloud will continue to grow in popularity and its security improve, it is integral that companies understand all of the risks involved with using a cloud-based solution, including questions around data ownership, and just how to secure the data.
Why You Need a Cloud-Based Secure File Transfer Solution
When you understand the inherent risks posed by unsecured devices and tools, the task becomes finding the best option for securely sharing your data. Enterprises need a secure file transfer tool that is not only top-notch when it comes to security, but also organizes and moves data at the speed of business. It also provides a secure file sharing application that supports the employee, customer, and trading partner collaboration critical to businesses today.
An enterprise-grade file sharing solution provides several key benefits, including:
► Data security, eliminating security gaps and governance challenges with structured access control
► Collaboration, connecting internal and external file sharing and collaborative workflow s
► Auditability, tracking all files that are received by or sent from your organization
► Scalability, to grow and flex with your business
With the right tool, your business will gain a modern way to control file sharing, messaging, and file transfer, all from a single platform. That’s why your secure file exchange system should feature:
► Advanced encryption for data in motion and at rest
► Structured user authentication
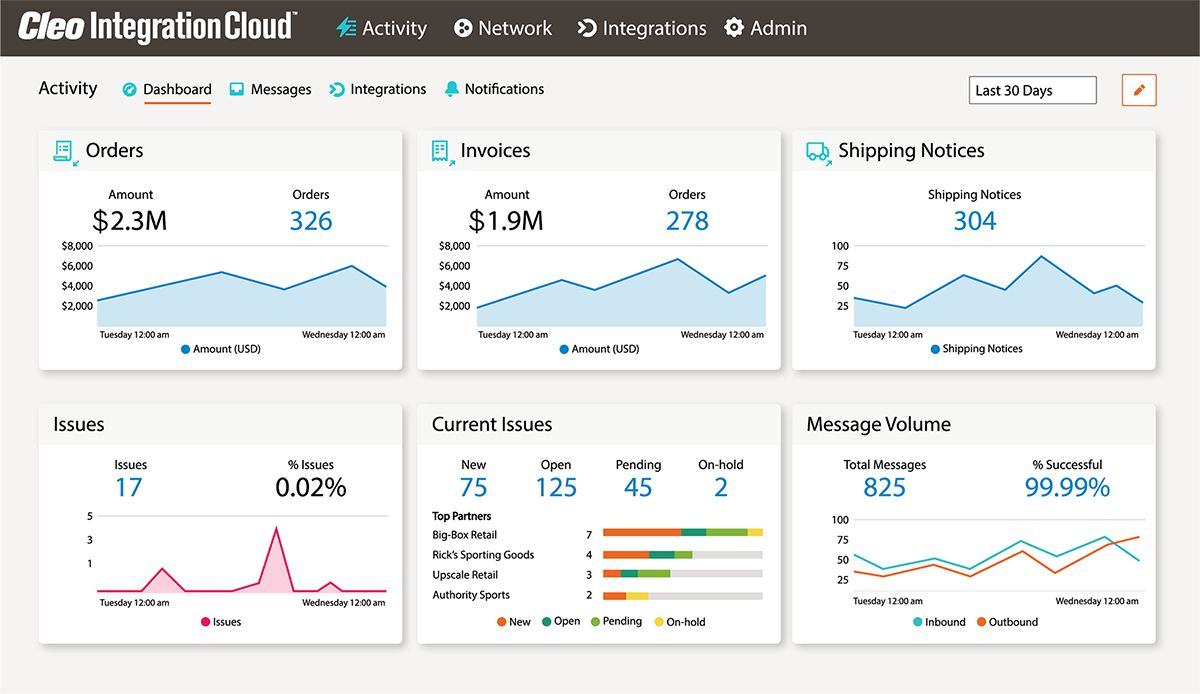
► Advanced logging, reporting, and dashboard tools
► Process automation capabilities
► Virus scanning and data loss prevention (DLP) features
The Best Secure File Sharing Platform
A secure, reliable, and scalable managed file transfer (MFT) solution quickly connects to internal systems and your business ecosystem, while moving data quickly and remaining compliant across all data interactions.
A few of the business-friendly file-sharing capabilities built into a leading MFT solution include:
► Robust data movement: MFT solutions feature an unprecedented depth of protocols and data connectors that extend simple file sharing capabilities and enable organizations to facilitate seamless internal and multi-enterprise data flows.
► Consolidation: Enterprises can consolidate all ecosystem, application-to-application, multi-cloud, and other business-oriented file-based integration processes onto a single platform for central control and management.
► Dashboards: Easy-to-use dashboard and visibility tools to track all data flows and access and provide business intelligence to a variety of personnel. Such capabilities also streamline auditing processes for more regulated industries like healthcare and financial services.
► Process automation: An MFT solution that leverages APIs to easily build, transform, and automate integrations, as well as programmatic file flows, is essential to enabling file-based integration processes between applications and in multi-enterprise B2B patterns within a larger hybrid integration strategy.
The days of “unmanaged” file sharing processes should be long over. An MFT platform with built-in file sharing capabilities reduces the risk of a data breach as well as potential non-compliance of customer SLAs.
Enterprise File Sharing Tools with Cleo Integration Cloud
Cleo Integration Cloud features a centralized platform that governs and secures all your managed file transfer and ecosystem messaging needs. With pre-built connectors that allow you to start transferring files in hours, secure file transfer protocol (secure FTP) support for all your trading partners, and an enterprise-ready secure file sharing application, the Cleo Integration Cloud Platform gives you the complete and total control you need to manage all your important business data flows.
Businesses gain true end-to-end visibility and audibility over all of their mission-critical data flows and can rest easy knowing that their data (and their customers’ data) is protected and compliant with industry mandates and partner SLAs.
The risks are out there; don’t hesitate and put your company’s data – and reputation – in danger. Schedule a demo with Cleo today and learn how enterprise-grade secure file sharing is key to a modern business integration strategy.

About Cleo