Blog: Are Retailers Actually Securing All Holiday E-Commerce Data?

This time of year, online retailers often spend heavy focus on the security of their web presence, PCI compliance in payment transactions, fraud detection, and so forth. The holiday season brings so much credit card and other payment activity that it’s a no-brainer for hackers to go after these types of e-commerce businesses during this time of year.
There’s an entire industry that helps retailers rightly focus on getting those things right. To comply with PCI standards, organizations must secure the processing, storing, and transmission of credit/debit card information, for their own protection as well as their customers’.
But even aside from the fact that overall PCI compliance is relatively low, one of the most important security concerns online retailers often overlook is the handling of sensitive data (consumer and otherwise) passed between suppliers, partners, and even cross-departmentally within the enterprise as various teams collaborate. In fact, there’s not a single digital transaction that doesn’t involve data moving from one place to another. And what happens once sensitive consumer information goes beyond an online portal or form?
How Data Breaches Happen
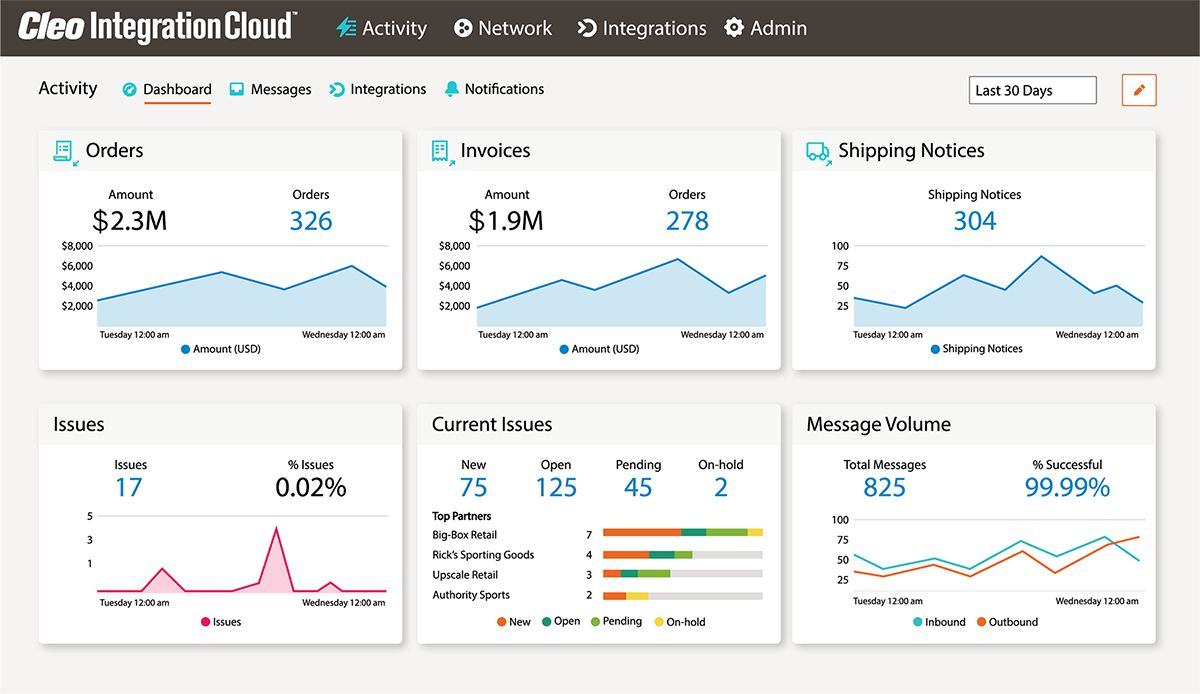
Being able to govern and track this holiday e-commerce data, and control who has access and where the data resides, should be as equally important as protecting static payment data, especially in an omni-channel supply chain. The truth is, a lot of these issues end up on the back burner while more successful online retailers scramble to cope with the sheer volume of data being handled and processed – and this is well before mentioning any notion of “big data.”
Breaches via third parties (often vendors and suppliers with access to the retail firewall) are some of the most common. If all parties involved are connected securely, data breaches would be greatly limited. But many retailers have to play catch-up and plug holes in their own networks (as well as their partner networks) instead of proactively implementing a secure managed file transfer (MFT) strategy.
Also, as business practices involve collaborating team members within the enterprise and beyond – company headquarters sharing stocking data, company forecasts, and even personal HR documents among geo-distributed locations, for instance – control of data must be maintained despite more empowered (and sometimes rogue) team members who might unwittingly introduce consumer-grade cloud-based sharing applications to get things done, at the expense of data security and governance.
Securing E-Commerce Data
But what if your online retail business, built on a highly secure data integration platform, offered an equally secure pipe for all of these transactions to take place?
As data is sent B2B to suppliers and partner firms, you need to meet some base-minimum security basics:
- Transacted and transferred data (not just card payments) are properly encrypted with digital signatures and tracked.
- Data will never reside inside the DMZ (encrypted or not). It’s not about really great encryption, it’s about not keeping data where it’s vulnerable.
- Data never moves to consumer-grade cloud storage.
Businesses must have proper security in place for their e-commerce data in motion, and companies using secure business data movement technology to help protect information once it is captured are ahead of the curve. While the holiday e-shopping rush is a good time to revisit a company’s cybersecurity strategy, it’s also a good time to drive the change needed to implement stronger technology and do better business all year long.

About Cleo