Secure Data Exchange Protocols
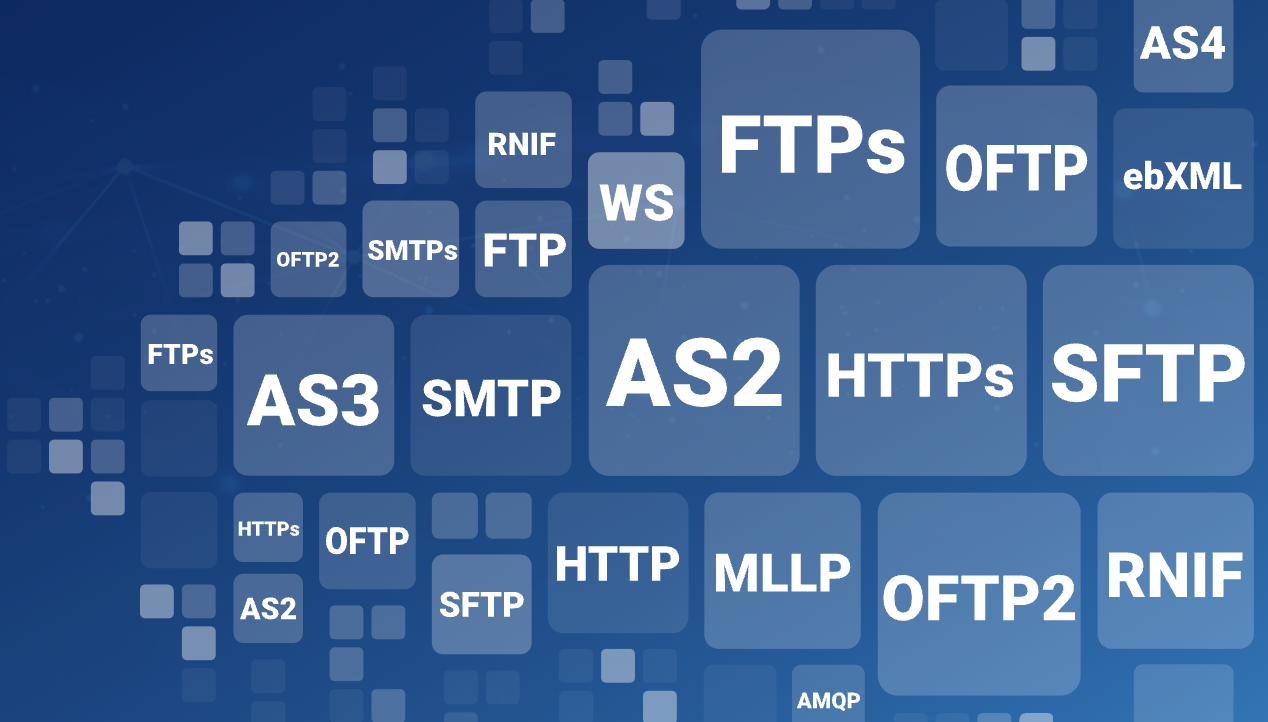
Cleo’s deep protocol flexibility enables robust B2B/EDI connection and integration capabilities, giving your business a competitive advantage.
Power your most critical business exchanges and securely connect to your customers, suppliers, and partners via Cleo's industry-leading integration solution.
Frequently asked questions
Learn more about common network security protocols.
What is a messaging protocol?
File transfer protocols, sometimes called EDI messaging protocols, act to transfer files both internally and externally to business customers, suppliers, vendors, and other network trading partners.
What does a file transfer protocol standardize?
B2B/EDI protocols standardize content and format. They further enable secure file transfer and data transport by outlining a standard procedure for regulating the data exchange internally and between businesses. A secure file transfer protocol acts as a set of rules that enable B2B and technology connection and data sharing.
What are the business requirements?
Protocols and standards differ across industry lines. And while protocols are sets of rules, individual organizations determine which set to use based on their own industry and compliance needs. As this implies, there are many file transfer protocols used to communicate today.
What are the benefits?
The main advantages of sending and receiving files over a secure file transfer protocol are the ability to:
- Transfer data internally and outside the firewall
- Automate transactions and eliminate errors
- Increase reliability and scalability
- Securely share business intelligence
- Meet compliance and SLA requirements
What does protocol flexibility mean?
Protocol flexibility becomes increasingly important as your network of trading partners and customers grows.
Understanding your current and future connectivity needs — including file sizes, volumes, transfer frequency, and security requirements — will help your organization select the best protocols.
Why is it important to used certified solutions for file transfer?
Certification with governing bodies or interoperability testing groups ensures the promised performance of a protocol and reduces setup time when both the sending and receiving parties are utilizing the same specifications and optional protocol functionality.
Cleo's products and standards have passed performance and quality assurance tests required for certification, allowing you to leverage the latest advancements in security and efficiency.

Our credentials
Cleo is committed to providing high-quality products and services. Cleo Integration Cloud is secure and tested against industry standards and is designed for data security and process integrity.